Ihr zertifizierter Atlassian Gold Solution Partner
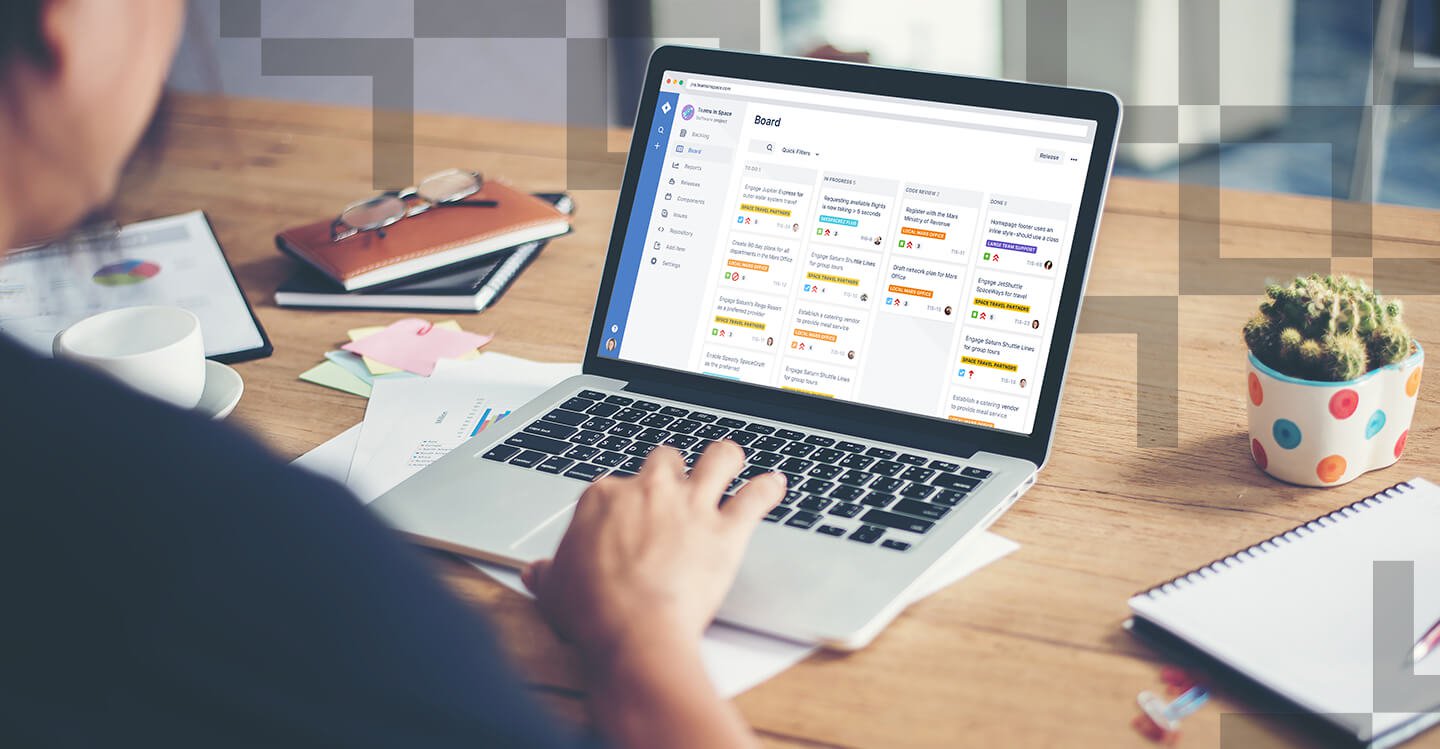
Effiziente Zusammenarbeit ist der Schlüssel zum Projekterfolg. Deshalb vertrauen tausende Teams weltweit auf Atlassian-Produkte wie Jira, Confluence und Bamboo, um ihre Arbeitsprozesse zu vereinfachen, den Wissenstransfer zu erleichtern und das Projektmanagement zu verbessern. Als zertifizierter Atlassian Gold Solution Partner können wir Sie bei der Auswahl, Anpassung und Implementierung der richtigen Atlassian-Tools unterstützen, damit Ihr Projekt ein Erfolg wird.